Wikileaks has just released a first part of a series of what purports to be a large collection of CIA documents documenting their hacking tools. See Vault7, as they call the whole leak. Numerous news organizations like the New York Times are reporting on this and saying they think they might be “on first review”.
If the leaked documents are genuine there are a number of interesting points to be explore:
- A Wikileaks notes, many of the hacks aren’t secret or copyrighted as they need to be placed on target computers.
To attack its targets, the CIA usually requires that its implants communicate with their control programs over the internet. If CIA implants, Command & Control and Listening Post software were classified, then CIA officers could be prosecuted or dismissed for violating rules that prohibit placing classified information onto the Internet. Consequently the CIA has secretly made most of its cyber spying/war code unclassified. The U.S. government is not able to assert copyright either, due to restrictions in the U.S. Constitution. This means that cyber ‘arms’ manufactures and computer hackers can freely “pirate” these ‘weapons’ if they are obtained. The CIA has primarily had to rely on obfuscation to protect its malware secrets.
- More disturbingly, many of these documents and associated code seem to have been circulating in US surveillance circles. Has the CIA lost control of its tools to their contractors? Are these now being used by others?
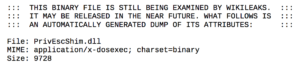
- Wikileaks is redacting the documents of names and withholding the code for the moment. (You can see an example of what you get if you try to download a DLL at the top.) There is, however, example code in the wiki pages at the bottom, but it seems mostly examples of how to do things rather than useful tools. They are also working with news organizations – I think they have learned from the Snowden leaks on how to dribble out large collections.
- Many of the documents seem to have been transcribed rather than reproduced. By that I mean that they appear as web pages in the Wikileaks site, not as they might have appeared originally. Again, see all the final wiki pages. Is this for ease of consultation, or to hide forensic evidence?
- Two tools/sites that are mentioned, but I can’t figure out are DART (could it be D.A.R.T. or Data Analysis Reporting Tool) and Devlan or devlan.net (both of which don’t result in much.) I’m probably misinterpreting things, but devlan.net seems to be the CIA server where a lot of stuff is located. See the RoidRage document.
- Of course, it should be noted that now the CIA seems to also be in the hacking game, along with the NSA. How much is being spent now? Do we actually feel any safer?
The overall impression I get reading through this stuff is that the days of solitary cyberhackers are passing. It takes an industrial approach with large teams building/maintaining/cloaking tools to be able to hack at will. That then increases the chances that the tools and techniques will leak out. The vaccine becomes the epidemic. What country can not afford to build some sort of cyberwarfare (or cyberdefense) network? As we build these networks we then build the infrastructure of educational and commercial support that ensures this new cold war will be played for decades. Should we be thinking of cyber-disarmament before it gets too late? According to la Repubblica the motivation of the source of the leak was explained thus by Wikileaks,
“The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons”.